
Vishing Detection and Prevention: A Guide for MNOs, MVNOs, and IPX Providers
Knowledge base
Share
Vishing, also known as voice phishing, is a significant cybersecurity threat, particularly within the telecom industry, including MNOs, MVNOs, and IPX providers.
Vishing fraud costs individuals and organizations staggering amounts each year. In 2023, more than 56 million people in the US (about 21% of the country’s population) lost $25.4 billion in telephone scams. Globally, the annual cost of cybercrime, including vishing, is projected to reach $15.6 trillion in 2029.
For the telecom industry, which not only facilitates but also depends on voice communication, implementing robust strategies for detecting and preventing vishing is essential for maintaining its integrity and long-term survival.
Unlike traditional phishing, which relies on written communication, vishing employs voice—a more direct and persuasive method. The personal approach, immediacy, and confrontation used in voice phishing often pressure victims into sharing sensitive information with scammers.
Additionally, CLI spoofing techniques make voice phishing difficult to identify for both telecom operators and customers. The advancement and widespread use of AI technologies—such as deepfake voice generation and voice cloning—further enhance the credibility of vishing scams.
This erosion of trust affects not only MNOs and MVNOs but the entire voice-based telecommunications sector. Customers simply no longer pick up the phone, which, in turn, leads to a decline in voice traffic revenue.
What is Vishing?
Vishing is a form of social engineering attack conducted over the phone, where fraudsters manipulate individuals into sharing sensitive information—such as login credentials, personal details, or financial data—or transferring money to them.
Voice phishing may seem too simple to work, yet it continues to grow as a significant threat to both telecom providers and individuals. Fraudsters frequently impersonate legitimate businesses or institutions, such as banks or government agencies, and may even act as distressed family members to exploit victims' emotions.
To make their scams more convincing and personalized, vishing fraudsters now use increasingly sophisticated techniques, including AI-generated deepfakes and voice cloning. These advancements have dramatically increased the success rate of vishing attacks, causing more harm to consumers and telecom operators alike.
For telecom providers, creating a robust vishing protection strategy should be a top priority.
Smishing vs. Vishing
Vishing (voice phishing) and smishing (SMS phishing) are two types of phishing scams that share common objectives but differ in their medium and tactics:
| Vishing | Smishing | |
| Objective | Trick individuals into revealing sensitive information, transferring funds, or installing malware. | Trick individuals into revealing sensitive information, transferring funds, or installing malware. |
| Medium | Conducted through phone calls, often using a spoofed number to obscure the call's origin. | Typically involves a URL link leading to a phishing site, delivered via SMS. |
| Tactics | Attackers impersonate trusted entities like banks, telecom providers, government agencies, and even family members. They create a sense of urgency or fear by claiming issues like unpaid bills or suspicious account activity. The goal of these scam calls is to extract sensitive information, such as passwords, payment details, or access codes. | Attackers send seemingly legitimate SMS messages containing malicious links or instructions. These messages often mimic service alerts, package delivery updates, or promotions, prompting recipients to click on links that lead to spoofed, legitimate-looking websites designed to steal information or install malware on devices. |
| Telecom-Specific Threats | When users fall victim to vishing attacks, telecom providers can suffer reputational damage. Attackers may even impersonate MNOs' customer service or technical support. Compromised VoIP systems can be exploited to launch additional vishing campaigns, increasing operational risks and costs. Operators may also face regulatory scrutiny and fines if they fail to protect customers from voice phishing attacks. Additionally, as trust in voice-based communication erodes, operators experience a decline in voice traffic revenue. | Smishing campaigns often exploit telecom infrastructure by sending fraudulent messages in bulk, potentially causing service disruptions or regulatory fines. Customers may also associate the telecom provider with the attack, damaging brand reputation and trust. Enterprise customers may shift OTP and 2FA procedures to alternative channels, leading to a reduction in lucrative A2P revenues. |
Fraud calls involve real-time interaction and are generally more resource-intensive for fraudsters—but they can also be harder to identify as they unfold. On the other hand, smishing relies on bulk messages and user action, giving victims more time to assess the legitimacy of messages.
Understanding these differences helps you design targeted cybersecurity measures and training programs to protect your infrastructure.
Vishing Tactics: Business Impersonation, Persuasive Scripts, and Emotional Manipulation
To defraud victims, scammers often impersonate reputable organizations, relying on targets’ trust in them. They frequently spoof caller IDs to display the name or number of the organization they are pretending to represent.
For example, a victim might receive a call from someone claiming to be a bank employee, warning of suspicious account activity and requesting account details or a one-time password. Fraudsters are skilled at making such situations feel real and urgent, causing victims to panic and react before they have time to think.
Vishing attacks are designed to prey on emotions and exploit human psychology, particularly the tendency to trust voice communication more than other types of interactions. To manipulate their victims, scammers often use well-rehearsed scripts to create a sense of urgency, fear, or excitement.
For instance, a scammer might inform the victim of suspicious activity on their bank account, claiming they need to verify personal information immediately to block unauthorized access. Or they might use a cloned voice to call someone's parents, pretending to be in an emergency and urgently needing money.
The goal of any vishing attack is always to create pressure or distraction so the victim complies without questioning the request.
The Role of AI and Deepfakes in Vishing Attacks
Voice phishing attacks are becoming increasingly sophisticated with the development of AI—scammers can now create carbon copies of anyone’s voice, producing highly convincing impersonations of trusted individuals or authority figures.
This technique is not new, but technological advancements will only make it more difficult to detect.
As early as 2019, fraudsters used AI to mimic the voice of a German energy firm's CEO, convincing the UK subsidiary's CEO to transfer €220,000 to a fraudulent bank account. More recently, a bank manager in Hong Kong received a deepfake video call appearing to be from the company's CFO, leading to a $25 million transfer to the fraudsters.
Why Vishing Relies on CLI Spoofing
Caller Line Identification (CLI) spoofing is often used in vishing scams to manipulate the perceived origin of a phone call. It enables scammers to falsify caller ID information and impersonate legitimate businesses, institutions, or even personal contacts, bypassing victims’ skepticism.
CLI spoofing is particularly dangerous in vishing fraud because it breaches victims’ initial trust barrier, making them even more susceptible to the scam.
Neighbor Spoofing, International Calls, and Roaming
Attackers may spoof local numbers similar to the recipient's area code or prefix. This exploits individuals’ tendency to trust local numbers more readily, assuming the call could be from a neighbor, local business, or community service. For telecom operators, this type of spoofing can remain undetected, as it appears less suspicious in bulk analysis. Spoofing is also used to avoid international termination rates.
CLI spoofing is sometimes used to mimic international numbers, particularly when targeting businesses that have global clients. This type of vishing attack increases costs for telecom operators, as carriers must handle inflated call volumes and address potential abuse of interconnection agreements.
Alphanumeric vs. Long-Code Caller IDs
Alphanumeric Caller IDs (where subscribers see the caller ID as, for example, "First Bank" instead of a phone number) are often used by legitimate businesses to increase the likelihood of actually reaching their customers.
However, attackers may exploit the lack of universal standards for verifying alphanumeric IDs, particularly in international calls, and spoof caller IDs to make them look like those of a familiar company or institution. The result? Trust in telecom service providers is further eroded.
Similarly, subscribers might perceive spoofed longcode numbers (for example in a 10-digit format) as more authentic even though they also evade basic anti-fraud mechanisms.
The Growing Ease of Spoofing on SIP and VoLTE
SIP (Session Initiation Protocol), which is widely used for VoIP, lacks inherent CLI authentication mechanisms, making it particularly vulnerable to spoofing. Attackers can easily manipulate headers to falsify caller information when making fraud calls.
And, while VoLTE offers improved call quality and efficiency, it’s reliant on SIP for call setup – meaning that it is especially vulnerable to spoofing. Spoofing tools are now more accessible, allowing even low-skilled attackers to target VoLTE networks without specific telecom knowledge or access.
Telecoms deploying SIP and VoLTE systems therefore face a double challenge: Ensuring their systems and infrastructure (for example, 5G) are scalable and can be deployed rapidly and also incorporating CLI authentication frameworks like Secure Telephone Identity Revisited (STIR) and Signature-based Handling of Asserted Information Using tokens (SHAKEN).
Notable Vishing Attacks and Their Impact
Let’s take a look at two notable phone phishing incidents that have significantly impacted the organizations that fell victim to them.
The sophisticated vishing fraud methods cybercriminals used in these examples highlight the extent of the problem and the profound consequences of such security breaches on organizations and the industry.
MGM Resorts Cyber Attack (September 11, 2023)
On September 11, 2023, MGM Resorts fell victim to a devastating vishing-implemented cyber attack, severely affecting business operations. The voice phishing attack was initially announced via X (formerly Twitter), where it was stated that the majority of MGM Resorts’ systems were compromised.
The vishing scam call attack's effects were immense; customers immediately began to face issues, from malfunctioning slot machines, online booking system failures, and digital key malfunctions at several MGM properties in Las Vegas. As a result, guests were prevented from entering MGM Resorts’ properties or making card payments, and all personal data stored by MGM was put at risk.
For this vishing attack, ransomware gang ALPHV, also known as BlackCat or Scattered Spider, identified an MGM Resorts employee via LinkedIn and then used vishing and social engineering to gain access to the company’s computer systems. The incident caused significant financial repercussions, including a 6% drop in MGM's share price.
Retool Spear Phishing Attack (August 29, 2023)
Developer Retool announced a data breach caused by a vishing attack on one of their employees, consequently impacting 27 cloud customers. Interestingly, the attack began with SMS-based phishing, where healthcare coverage was used as a reason for the interaction. The elaborate attack method eventually led to a vishing phone call, where the attacker used deepfake technology to impersonate an IT staff member’s voice.
The vishing scam call attack resulted in the takeover of a Retool employee account. The company’s internal administrator systems were compromised, leading to fraudsters obtaining valuable and sensitive data.
Retool responded by deactivating all internal authenticated sessions and blocking all affected accounts.
Key Vishing Tactics Used in These Cases
These high-profile attacks demonstrate the evolution of vishing tactics, including:
- Spear phishing: Targeting specific individuals via SMS or email before escalating to vishing calls.
- Impersonation scams: Fraudsters posed as trusted IT staff to manipulate victims into revealing credentials.
- Deepfake-enhanced vishing: AI-generated voices made attacks more convincing.
- Social engineering through LinkedIn & public data: Attackers researched victims' roles and responsibilities before targeting them.
- Multi-stage fraud: Scammers first used SMS phishing (smishing) before following up with vishing calls.
Such vishing fraud is reliant on vulnerabilities, a lack of staff awareness, and our trust in the people and voices we know – and can cause significant and irreversible damage.
The Cost of Vishing and Voice Fraud
Vishing, or voice phishing, incurs massive financial, reputational, and operational damage across the entire telecommunications ecosystem and impacts everyone: subscribers, enterprises, and telecom operators.
It’s difficult to estimate the total global cost of vishing, but we have a number of indicators at our disposal that help us better grasp the seriousness of the problem:
Globally, scams and identity fraud have cost victims $1.026 trillion annually (GASA 2023). For telecoms, fraud-related losses in 2023 sit at an estimated $38.95 billion.
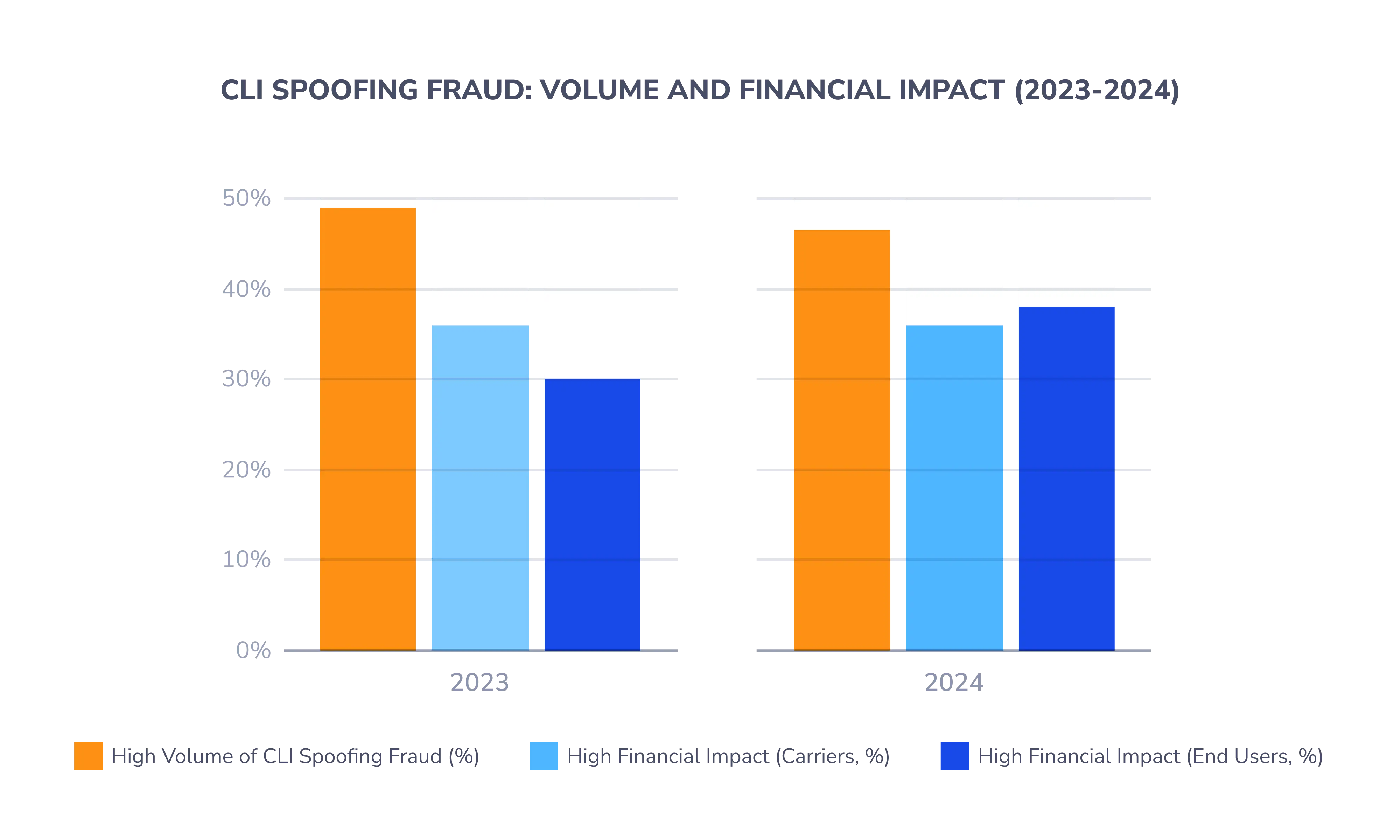
A significant portion of telecom fraud comes from phone scams, which have become more advanced and widespread. Caller ID (CLI) spoofing has accounted for more than $2.6 billion in losses in 2021, according to data from the Communications Fraud Control Association (CFCA).
According to the Social Engineer LLC’s State of Vishing 2023 report, the total financial loss due to imposter phone scams in the US was $1.2 billion for the year, while 39% of vishing calls lead to a data compromise between 2020 and 2022. The Consumer Sentinel Network (CSN), a secure online database managed by the US Federal Trade Commission (FTC) is reporting more than 850,000 imposter scams in 2023 alone.
According to a recent report by Juniper Research, mobile subscribers worldwide were projected to lose $58 billion to fraudulent robocalls in 2023. Additionally, Wangiri scams, which trick victims into returning costly international calls, cost $2.23 billion in 2021, according to the CFCA 2021 Global Fraud Loss Survey.
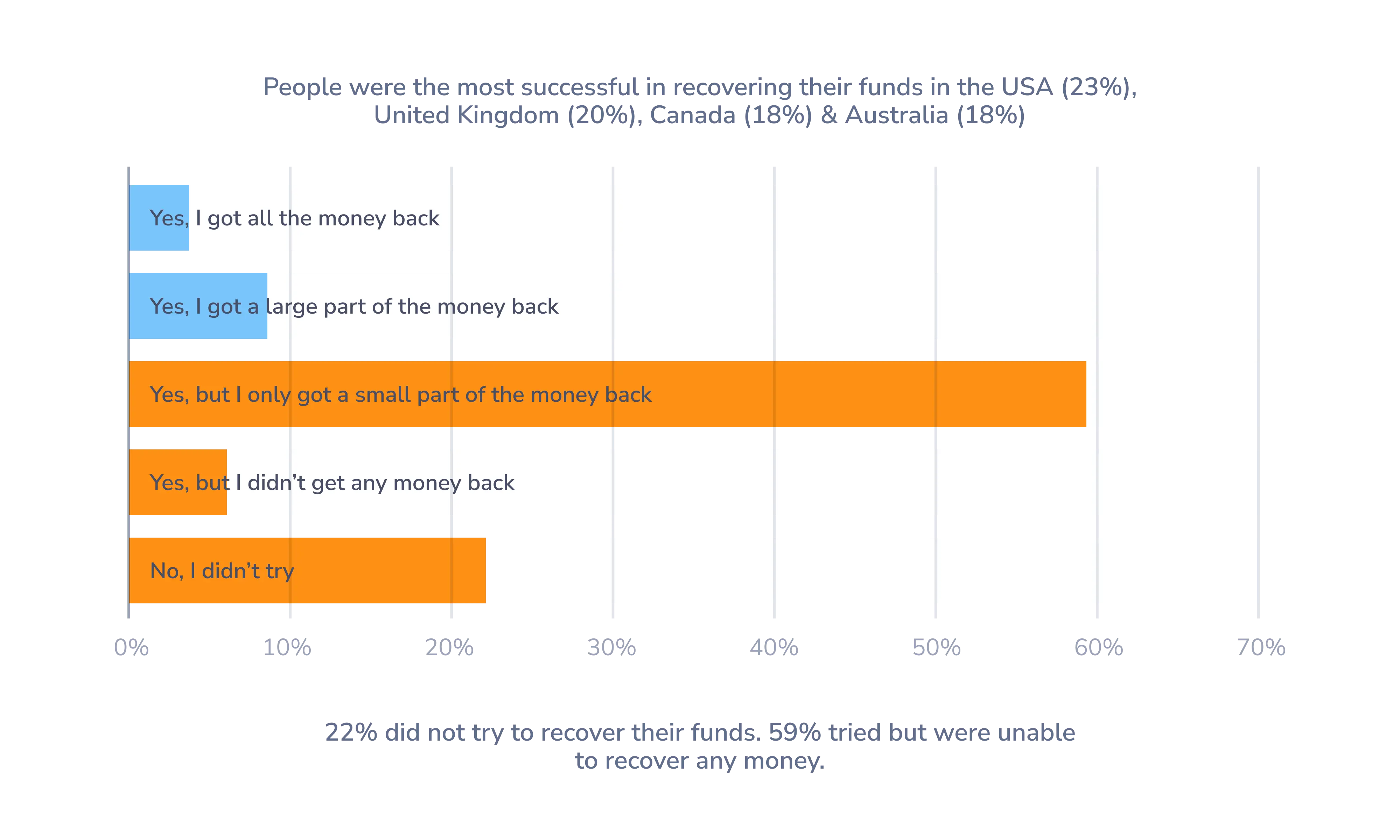
However, these attacks result in more than financial harm; they also erode consumer trust. For telecom operators, this lack of confidence directly impacts revenue. Wary subscribers start to avoid answering calls altogether or engaging with voice-based services. In fact, 25.5% of the global population has suffered financial losses from scams or identity fraud – so trust in voice communication is likely at an all-time low.
It’s clear that phishing phone calls are a massive problem for telecom operators everywhere. Vishing fraud has now evolved into a global epidemic that costs billions and undermines trust in critical communication systems. So, addressing this issue isn’t merely about reducing telecoms’ and individuals’ losses – it’s also about restoring customer confidence in telecommunications infrastructure and voice-based services.
Other Types of Voice Fraud
Voice fraud comes in many forms, each designed to exploit specific vulnerabilities in the telecom ecosystem, from tariff structures to interconnect agreements and customer trust.
The cumulative effect includes lost revenue, network inefficiencies, and damaged subscriber trust. Addressing these threats requires advanced fraud detection systems, real-time traffic monitoring, customer vishing prevention strategies, and collaborative efforts between MNOs, regulators, and enterprises.
Here are the types of voice fraud and scam calls you should be aware of:
Robocalls and Spam Calls
Robocalls or spam calls consist of high volumes of automated calls, often with pre-recorded messages, with the goal to scam, defraud, or harass subscribers. Similarly to vishing, fraudsters may use robocalls to impersonate banks or government agencies, pressuring victims to divulge sensitive information.
These calls degrade the user experience, increase customer complaints, and contribute to a growing distrust in voice services, which, again, reduces overall call traffic.
IRSF and Wangiri
In IRSF (short for International Revenue Share Fraud), attackers generate fraud calls to international premium-rate numbers they control, inflating traffic to earn revenue from termination fees.
As a result, MNOs may face huge termination costs and are often unable to recover them.
In Wangiri fraud, attackers place short calls to trick users into calling back premium-rate numbers. This results in subscribers bearing unexpected charges, while MNOs are stuck managing disputes and absorbing operational costs.
Learn more about how Wangiri scams work and how to prevent them in our article, Wangiri Fraud Prevention and Detection.
Short Stopping, Arbitrage, Call Stretching, and Hijacking
Short stopping involves terminating traffic at an intermediate destination instead of the intended one, allowing fraudsters to pocket the difference in termination fees. Need more info on short stopping fraud? AB Handshake’s article, What is Call Short Stopping Fraud, explains its effects on telecom operators and offers strategies for prevention.
Call stretching refers to the act of artificially extending call durations to increase billing revenue. Read more about this fraud type and fraud mitigation techniques in the AB Handshake article, Call Stretching & Short Stopping.
Arbitrage fraud involves scammers exploiting inconsistencies in call routing tariffs to generate illegitimate revenue by routing traffic through cheaper channels, while hijacking is the interception of legitimate calls and rerouting them for profit.
SIM Box Fraud
SIM cards meant for personal or regional use can be inserted into devices (SIM boxes) to place international calls as local calls, bypassing official interconnect rates.
MNOs lose termination revenue and, in parallel, face increased network congestion. Subscribers may also experience reduced call quality or service disruptions.
Read Interconnect Bypass and SIM Box Fraud Explained for more information on this fraud type and strategies for its prevention.
VoIP and OTT Bypass
In this type of fraud, voice traffic is routed through VoIP or over-the-top (OTT) apps to avoid interconnect fees. This means that MNOs lose out on traditional termination revenues.
The growing adoption of OTT services further shifts traffic away from operator-managed voice channels.
PBX Fraud (Dial-Through Fraud)
PBX fraud refers to the practice of exploiting vulnerabilities in private branch exchanges (PBXs) to generate unauthorized calls, typically to international premium-rate numbers.
As a result, enterprises face hefty phone bills, while MNOs must handle customer complaints and disputes.
Wangiri 2.0
This is an evolved version of the traditional Wangiri scam, which targets businesses. In Wangiri 2.0, fraudsters trick employees into calling back premium-rate numbers or create fake missed calls that might appear to come from suppliers or partners.
Flash Calls
Flash calls aren’t fraudulent as such but bypass the SMS A2P (application-to-person) ecosystem, eating into A2P messaging revenue for operators. Billed as an alternative to SMS, businesses send a zero-duration call to authenticate users instead of using SMS for one-time passwords (OTPs). Frequently, flash calls use spoofed numbers, however, they can also use legitimate number ranges.
Voice Fraud Regulations
Governments across the world have implemented different measures to combat voice fraud and scam calls. In this section, we’ll look into some of these regulations and what they mean for telecoms.
Is Spoofing Legal? Regulations Across Different Countries
Caller ID spoofing involves deliberately falsifying the caller ID information transmitted to a recipient to disguise the caller's identity. It’s often associated with fraudulent activities, but it can also serve legitimate purposes.
For instance, when calling customers, businesses may display their toll-free numbers or a central callback number to ensure consistency and recognizability.
In the US, under the Truth in Caller ID Act, it is illegal to transmit misleading or inaccurate caller ID information with the intent to defraud, cause harm, or wrongfully obtain anything of value.
In Canada, caller ID spoofing is generally legal unless it’s done with the intent to defraud or cause harm. Additionally, telemarketers are prohibited from using misleading caller IDs.
Australia enforces specific rules regarding caller ID information. The Telecommunications Act of 1997 requires that caller ID information must not be misleading or inaccurate. The Australian Communications and Media Authority (ACMA) oversees compliance and can issue penalties for violations.
The UK Government’s Fraud Strategy 2023 aims to tackle fraud at its source and pursue scammers and fraudsters internationally. The establishment of the National Fraud Squad presents a healthy step towards providing better support for victims and catching fraudsters.
Growing Regulatory Pressures on Telecom Operators
Governments and regulatory agencies have been increasing the pressure on telecom operators to tackle voice fraud.
MNOs in many countries face stiff fines for failing to protect their customers by preventing phone scams and vishing attacks. In the UK, for example, telecom companies may be fined up to 10% of their revenue for failing to adequately protect their customers from cybercrime.
Telecom operators in the US and Canada are also required to adopt STIR/SHAKEN to authenticate caller IDs, with non-compliance resulting in penalties. This is a significant step in authenticating and validating voice calls and has significantly reduced spam and fraud; however, achieving effective adoption of the protocol proved quite challenging.
Current Solutions to Spoofing and Vishing: Challenges and Limitations
To combat spoofing and vishing fraud, several solutions are implemented by telecom providers and technology vendors. However, these solutions also face some challenges that limit their effectiveness.
1. Consumer Education
Banks and governments are making efforts to educate consumers about spoofing and vishing scams through awareness campaigns. This can help users identify red flags, such as unusual requests, unfamiliar numbers, or situations in which the caller creates a sense of urgency and fear.
The challenge: Unfortunately, consumer education has limited impact because it relies on individuals to recognize and respond to threats.
Many users are either unaware of these campaigns or unable to apply what they’ve learned in high-pressure situations. This approach has been proven insufficient in reducing fraud significantly.
2. Detection Apps
Mobile apps like Truecaller and Hiya help identify and block spam and fraudulent calls with the help of user-reported databases. For this, they flag suspicious numbers as spam to warn subscribers.
The challenge: Detection apps depend heavily on consumer participation because their databases rely on users’ reporting. Additionally, many scams originate from legitimate-looking numbers that are difficult to block preemptively.
Furthermore, users must actively install and maintain these apps, which not all consumers are willing to do, and many don’t know such tools exist.
3. Verified Caller Registries
Caller registries are databases used to verify the authenticity of phone numbers. These registries allow telecom providers and enterprises to register their numbers, enabling better identification of legitimate calls and distinguishing them from fraudulent ones. The idea is that verified numbers provide a higher level of trust, reducing the likelihood of spoofed calls reaching end users.
The challenge: Caller registries verify numbers but do not prevent spoofing, as fraudsters can still impersonate registered numbers. Their effectiveness depends on widespread adoption, yet many businesses fail to register, creating gaps in protection. Additionally, frequent number changes make real-time updates difficult, limiting their ability to stop vishing and spoofing fraud.
4. STIR/SHAKEN
STIR/SHAKEN is a caller authentication framework designed to combat spoofing by verifying caller ID information at the network level. It works by attaching a digital certificate of trust to call metadata, ensuring that calls from registered numbers can be identified as legitimate. This system is particularly effective at reducing neighbor spoofing and other forms of fraudulent caller ID manipulation within networks that have implemented the protocol.
The challenge: STIR/SHAKEN is not globally adopted, leaving fraud calls from outside the U.S. and Canada unchecked. High implementation costs make it unaffordable for many MNOs, and it cannot stop spoofed legitimate numbers or VoIP fraud. Additional fraud detection is needed.
5. Number Validation and Intelligence
Number validation tools use real-time data to assess the legitimacy of incoming numbers. By analyzing call history, geographic origin, and patterns, they help identify anomalies that might be indicative of fraud.
The challenge: These services only catch spoofed calls that use fake numbers but miss the majority of vishing attacks, which use legitimate spoofed numbers. In fact, 75% of fraudulent calls spoof legitimate numbers and will not be flagged by number validation services.
6. Spam Labeling
Spam labeling solutions use analytics to flag likely spam calls, marking them on caller ID displays, for example, as "Suspected spam caller." This gives users a simple way to filter risky calls.
The challenge: This approach often results in over-labeling, where too many legitimate calls are flagged as spam. On the other hand, many labeling solutions are unable to detect spoofed calls, and failure to label these calls may actually lend more validity to the call.
This creates two problems: users either ignore warnings altogether or adopt a “never answer” approach, which impacts legitimate businesses relying on phone communication (and decreases voice traffic revenue).
7. Signaling Firewalls and SBCs (Session Border Controllers)
Firewalls and SBCs monitor signaling protocols to detect and block suspicious activity at the network level. They provide real-time protection by filtering out traffic that doesn’t meet predefined rules or traffic that surpasses volume thresholds.
The challenge: Firewalls often rely on reactive rulesets rather than proactive detection. They rarely include detection for sophisticated fraud patterns or spoofing attempts, which prevents them from effectively stopping many kinds of voice fraud. Rulesets are also prone to overblocking, causing unnecessary service disruptions and loss of revenue due to lowered traffic volumes.
Reports indicate that 23–25% of calls are falsely flagged in fraud management systems (CFCA Global Fraud Loss Report 2023).
How to Prevent Voice Fraud and Spoofing
So, how can vishing be prevented?
There are a number of steps communication service providers (CSPs) can take to tackle the problem of voice fraud, spoofing, and vishing.
Use Common Sense Filters, Rulesets, and GSMA Guidelines
First, start with implementing common-sense filters, using the GSMA guidelines to inform your efforts.
This strategy can help identify and block suspicious activity and involves setting clear rules to flag anomalous behavior, such as mismatched caller ID information, unrealistic call durations, or abnormal calling patterns. These can provide a foundational layer of fraud detection and reduce obvious fraud attempts – but do not address all fraud.
Use a National Anti-Fraud Platform
A national approach to vishing prevention centralizes efforts to secure voice traffic by fostering inter-operator support and collaboration among various stakeholders.
AB Handshake’s National Anti-Fraud Platform provides a framework for governments, enterprises, and all local telecom operators to work together in preventing voice and SMS impersonation fraud and spam.
The platform integrates with existing telecom infrastructures and enables real-time call validation by comparing call data from both the originating and terminating networks. Behavioral analysis of voice traffic further protects consumers and MNOs from international and wholesale fraud that does not rely on spoofing.
By addressing fraudulent activity at the national level, the system protects not just individual users but also critical sectors like government, finance, and healthcare.
AI Trained on Large Telecom Datasets
Artificial intelligence is an effective tool in identifying both simple and sophisticated fraud schemes with the highest precision. AI systems trained on large datasets can identify new patterns of fraud, predict attack methods, and detect anomalies in real time. Advanced AI reduces false positives and enhances the accuracy of fraud detection, allowing you to stay ahead of fraudsters and maximize the quality of service.
AB Handshake’s AI Shield helps telecoms reduce direct losses to fraud. This solution detects and blocks all major types of voice fraud attacks and enables you to protect your network and detect fraudulent calls with a 99.995% accuracy and therefore eliminate direct, operational, and reputational losses.
Call Validation (A&B Party Verification)
AB Handshake’s call validation technology provides a secure and transparent verification process for every call event, using a secure out-of-band query to perform end-to-end validation.
This process includes authentication of both the calling and receiving numbers (A and B numbers), employing a ‘virtual handshake’ that authenticates each call.
This method is necessary to successfully prevent CLI spoofing and a range of other fraud tactics, including vishing. Call validation helps protect consumers, enterprises, and MNOs while restoring trust in voice communication.
Why CSPs Should Combat Vishing and Voice Fraud
Network operators play a central role in the fight against voice fraud to protect their subscribers and maintain the integrity of their networks. There are several key reasons why this is crucial:
Enhancing QoS and Subscriber Experience
Eliminating voice fraud enhances the user experience and restores trust in voice-based services. By reducing spam and vishing attempts, network providers can deliver reliable and trustworthy communication services—improving customer satisfaction over time.
Restoring Trust in the Voice Communication Channel
Vishing and spoofing have gradually eroded public trust in voice calls—today, many users simply no longer answer calls from unknown numbers. Effective fraud prevention helps restore their confidence and encourages them to re-engage with voice services, increasing call traffic and revenue.
Protecting Enterprises with Enhanced Value-Added Services (VAS)
Fraud often targets businesses through schemes like PBX hacking and impersonation scams. By offering advanced fraud prevention as part of their VAS, CSPs can safeguard their enterprise customers, who are an important part of their customer base.
Strengthen Subscriber Trust and Protect Infrastructure Integrity
CSPs are uniquely positioned to combat voice fraud due to their insights into call signaling data and interconnect platforms, as well as their control over network infrastructure. They can implement effective fraud prevention measures, such as call validation and traffic monitoring, directly within their networks.
We’ve developed AB Handshake’s solutions to meet the specific requirements of MNOs, MVNOs, and IPXs to help combat vishing fraud attacks. This helps restore the integrity of your infrastructure and strengthens your subscribers’ confidence in voice-based communications and services.