
PBX Hacking Fraud Explained
Knowledge base
Share
Telecommunications fraud is a threat that continues to plague both service providers and end-users worldwide. One such fraud technique that has grown in recent times is PBX hacking fraud, often described as dial-through fraud. This type of fraud disrupts business communication channels and causes significant financial loss. In this article, we will explore the complex issues surrounding PBX hacking fraud, its impact on businesses, and provide actionable strategies for protection against such attacks. Continue reading to discover how to protect your organization from the dangers of PBX exploitation and ensure uninterrupted communications.
What is PBX Hacking / Dial-Through Fraud and How It Works
PBX hacking, also known as dial-through fraud, is a type of telephony fraud where criminals gain unauthorized access to a company's Private Branch Exchange (PBX) system. This access enables fraudsters to make long-distance or international calls with the charges billed to the compromised company.
In traditional telephony, PBXs (Private Branch Exchanges), are used as private telephone networks within organizations, connecting them to the Public Switched Telephone Network (PSTN) via Telecommunications Service Providers (TSPs) or Internet Service Providers (ISPs). Fraudsters attempt to find vulnerabilities, like poorly protected maintenance ports or weak security, to gain unauthorized access to PBXs for fraudulent activities. Such activities include making unauthorized calls, often to premium-rate numbers, known as toll fraud.
Toll fraud is a specific technique used in PBX hacking fraud, where attackers make calls to premium-rate numbers they own or have agreements with. These calls are often short, but the charges are excessive, leading to significant costs for the victimized company.
With the increasing adoption of IP-based PBX systems, an example of VoIP telephony, hackers target IP-PBX systems by exploiting software vulnerabilities and using techniques like password cracking to gain unauthorized access. Once inside an IP-PBX system, they use it to conduct PBX scams by making unauthorized VoIP calls at the company's expense.
Regardless of whether PBX systems are IP-based or circuit-based, they remain a prime target for voice fraud. One of the main reasons for their vulnerability is the lack of awareness among users regarding the risks of PBX hacking, leading to a failure to implement even basic fraud protection measures. For example, PBX users often leave default passwords provided by switch vendors unchanged during installation, making it easy for attackers to access the systems.
Examples of PBX Hacking
Scenario 1: Artificial Inflation of Traffic through Hacked PBX (Generated Traffic)
A common example of PBX fraud involves the artificial inflation of service usage, where traffic is generated using a hacked PBX, specifically in the context of international revenue share fraud (IRSF). This scenario involves artificial generation and short-stopping of traffic through the victim’s PBX, as shown in Figure 1
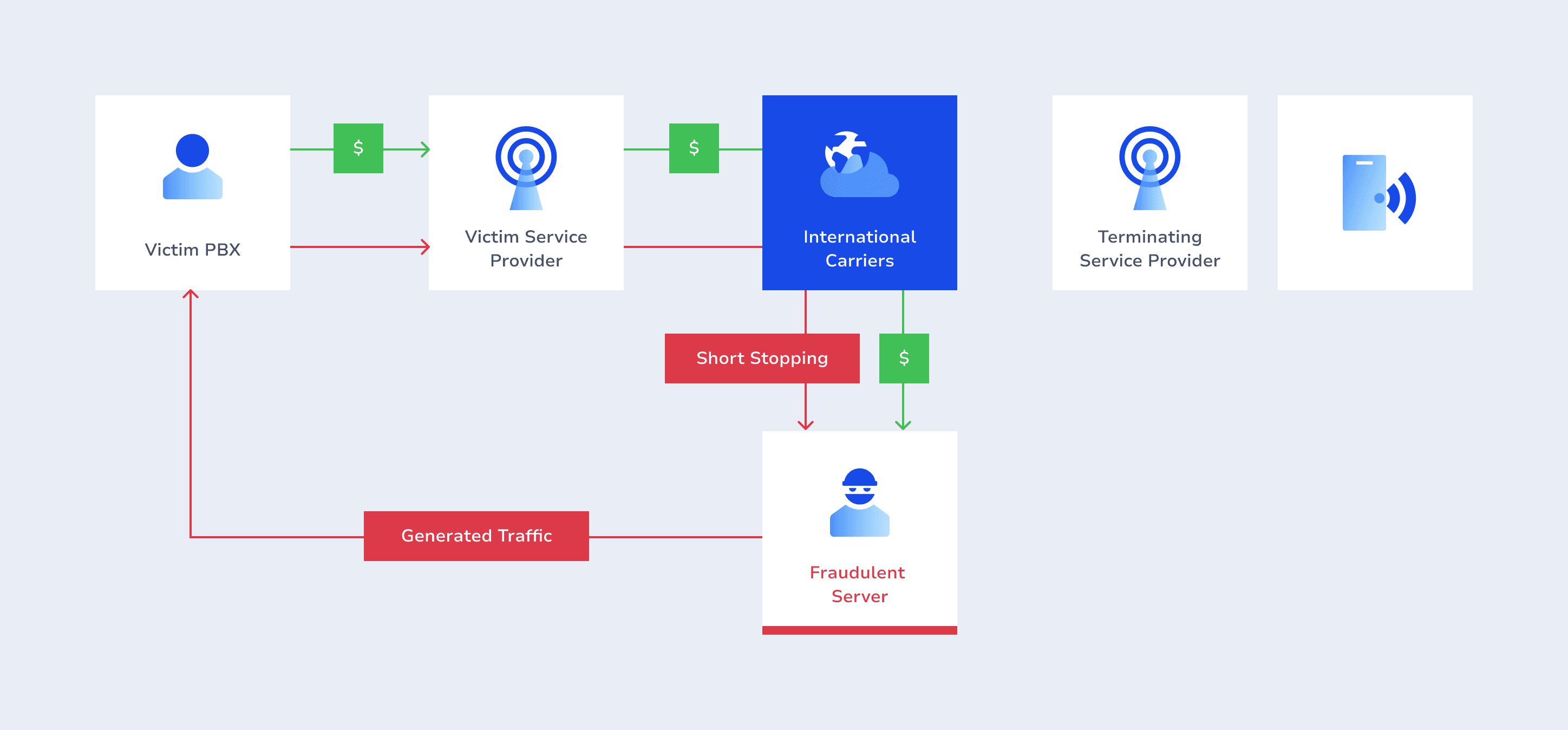
Generated traffic never reaches actual end-users. Instead, fraudsters intercept and reroute traffic in the cloud of international carriers. Consequently, payment streams are redirected from the legitimate victim’s service provider to an unethical carrier it cooperates with.
When this method is used, artificial calls give the false impression of a high volume of real calls, leading to inflated charges and financial losses for the victim organization. To combat this type of PBX fraud, organizations must implement reliable security measures, including regular PBX software updates, strong authentication mechanisms, and monitoring of call patterns and traffic flows for anomalies. By proactively implementing these security measures, businesses can significantly mitigate the risks associated with artificially inflated traffic.
Scenario 2: Fraudulent Routing of Traffic via a Hacked PBX
Another challenging fraud scheme involves the fraudulent routing of traffic via a hacked PBX. In this scenario, a fraudulent international transit carrier exploits the compromised PBX to divert legitimate traffic. The scenario works by routing calls from the originating service provider’s end users through the hacked PBX, ultimately delivering them to real end-users.
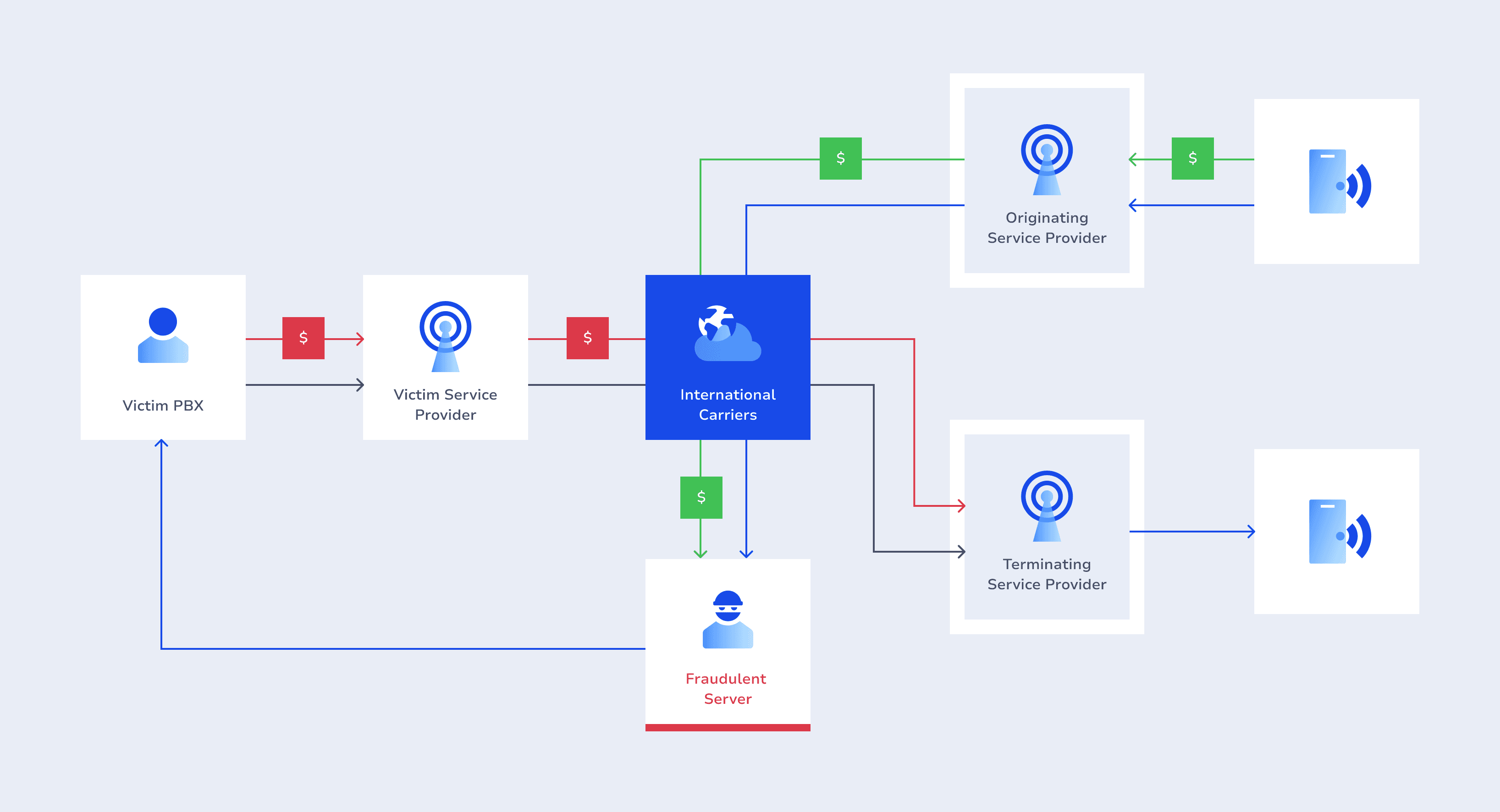
The genuine nature of this scheme makes it incredibly difficult to detect, as the traffic originates from legitimate sources. To the terminating service provider, the processed traffic appears entirely natural, with end-users making and receiving calls. Consequently, the victim service provider unknowingly bears the costs associated with this fraudulent traffic. Detecting and mitigating this form of fraud requires a proactive approach, including comprehensive security measures, vigilant monitoring, and collaborative strategies involving operators and transit carriers.
The Impact of PBX Fraud
PBX hacking poses a serious fraud risk to telcos, resulting in substantial revenue losses. According to the Communications Fraud Control Association (CFCA), PBX hacking ranks among the top five telecom hacking methods and emerging fraud risks to the telecom industry. In 2021, PBX hacking fraud resulted in $3.24 billion in losses, as reported by the CFCA.
AB Handshake’s findings also highlight the severity of the threat that PBX Hacking poses to customers worldwide. Our thorough analysis of over 200 million calls per day reveals the following:
- Over 7% of calls are either artificially generated calls from a PBX or calls routed through a PBX;
- More than 12 million calls per day worldwide are connected with dial-through fraud;
- More than half of PBX hacking calls and attacks are rated at medium severity, with over 30% classified as highly severe, potentially resulting in losses exceeding $10,000 per single attack;
- Most PBX attacks occur on weekends and dominate in regions such as Africa, followed by the Americas, and Europe;
- The regions most affected by PBX hacking are APAC, the Middle East, and Europe.
All the above underscores the importance of understanding the problem's impact on operators and taking measures to ensure the security of their networks.
Why Conventional Fraud Management Methods are Ineffective in Preventing PBX Fraud
PBX Hacking Prevention and Detection: AB Handshake’s Solution
AB Handshake recognizes how important it is for operators to retain corporate customers by providing the highest levels of service and security. We offer both protection against fraudulent traffic for operators and a tailored solution for their B2B customers. For operators seeking additional services for their B2B clients, AB Handshake can create system subaccounts for larger corporate clients to protect their traffic from fraud in real time.
The AB Handshake solution is based on AI Shield, an artificial intelligence module powered by machine learning. With over 200 parameters for traffic analysis, it detects even the smallest discrepancies in call patterns and blocks fraudulent calls in real time. With AI Shield, PBX Hacking is detected and blocked with 99.995% accuracy, ensuring the highest standard of protection for service providers and enterprises.
The tool is fully automated and pre-trained on large volumes of wholesale and retail traffic, ensuring optimal performance from day one.
AB Handshake’s Call Validation is another effective tool for detecting and blocking all instances of PBX hacking fraud, best suited for network operators and larger businesses. Call Validation works in real time to prevent all fraudulent calls from reaching the end user. Visit this page to learn more.
AB Handshake Call Validations success is evidenced through the urgent directives from the ITU CxO meeting 2023, advocating for a robust, globally coordinated approach to real-time call validation. The ITU CxO meeting attendess unanimously concluded that threshold-based rules were generally ineffective and, in isolation, certain solutions were also inadequate as a method of preventing fraud globally.
Gain insights into the ITU's concerted efforts against telecom fraud and see how these initiatives complement AB Handshake’s solutions.
For more details on AI Shield visit this page or get in touch to book a meeting with our team.