
Caller ID Spoofing Fraud Explained
Knowledge base
Share
Caller ID spoofing fraud, also known as CLI spoofing, CLI refiling, CLI overstamping, and call masking, is a growing concern for telcos, enterprises, and subscribers. This type of fraud involves manipulating the Caller ID to deceive the recipient about the caller’s true identity. The severity of the issue cannot be underestimated, as demonstrated by the following figures for 2021:
- Worldwide revenue losses to telecom fraud as a whole reached a whopping $39.89 billion;
- Losses to Caller ID spoofing fraud alone amounted to $2.6 billion.
Understanding the complexity of caller ID spoofing fraud is vital for protecting yourself from becoming another statistic. In this article, we explore this topic in-depth and provide effective strategies for staying informed and implementing measures to protect your telecommunications and personal information from the dangers of Caller ID spoofing fraud.
What is Caller ID Spoofing?
CLI spoofing, also known as Caller ID spoofing, is one of the most widespread types of telecom fraud, used in common fraud scenarios like robocalls, spam, one-ring scams, and vishing (voice phishing).
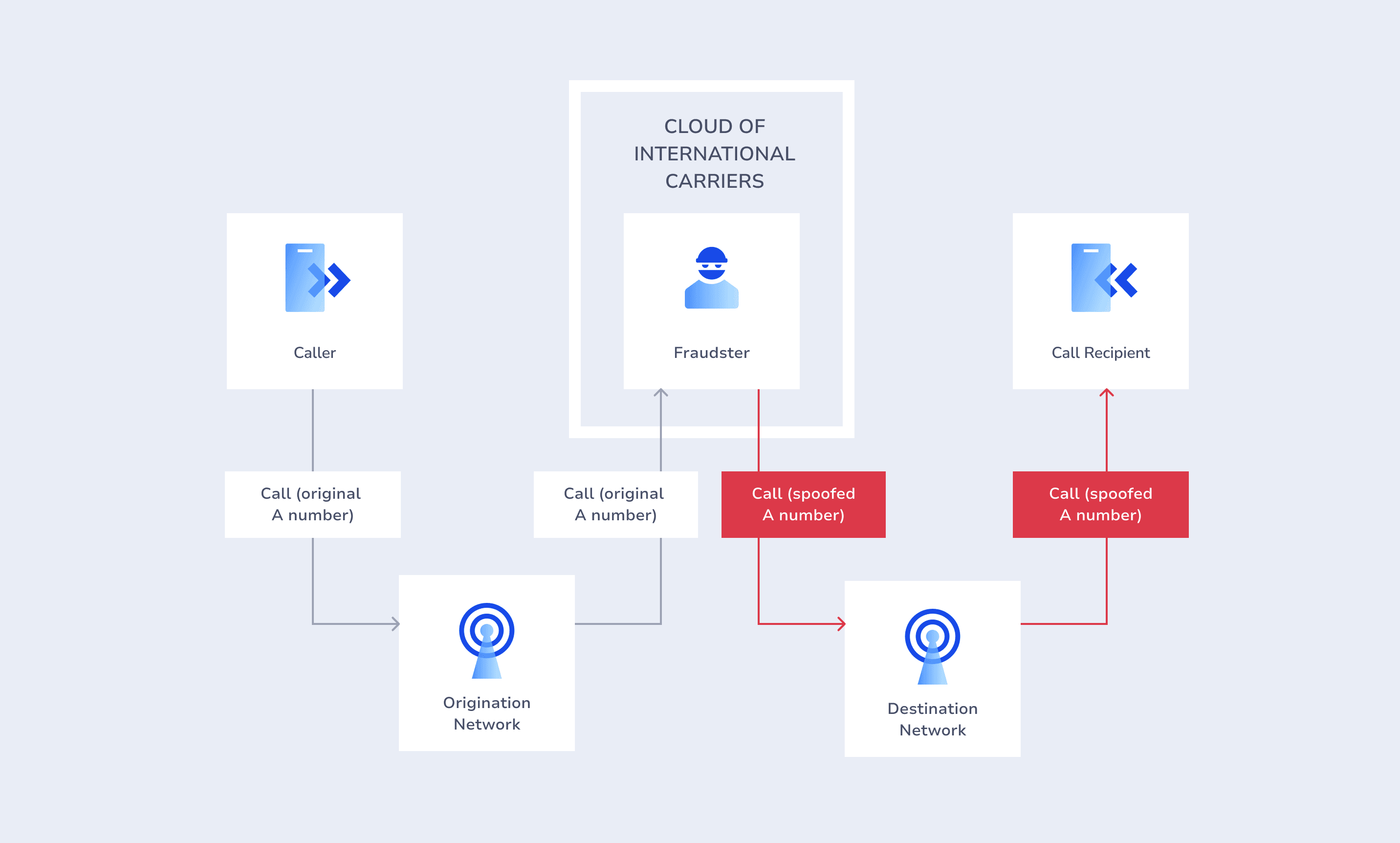
In Caller ID spoofing, fraudsters manipulate the caller ID (A-number) displayed on the recipient's phone, disguising their identity and making it seem like the call is coming from a local number or a trusted brand. This manipulation allows fraudsters to deceptively steal valuable personal information through the use of scripts without the victim’s awareness.
Another reason for A-number spoofing is to reduce the termination cost of international voice calls, especially when Origin Based Rating (OBR) or a specific roaming zone is in place at the target destination.
A subtype of “traditional” Caller ID spoofing is GSM spoofing, which involves falsifying the source address of an SMS or voice call by manipulating the parameters that identify the sender in the GSM network.
Caller ID Spoofing Fraud in Europe: OBR Rates Bypass
History of OBR in the EU: Where CLI Spoofing Comes From
To understand the story behind CLI spoofing fraud, we must first look at the history of termination rates and OBR in Europe.
Historically, EU termination rates ranged from between €0.01 to €0.15. In 2015, regulators forced termination rates down to €0.01 to unify the rates and allow residents of different EU countries to call each other at domestic-like rates.
This shift led to substantial revenue losses for local service providers.
Operators reacted and introduced the Origin Based Rating (OBR) model with higher rates for non-EU originating A-numbers, resulting in:
- Termination rates for non-EU A-numbers up to 50x higher than EU rates.
- A broad range of termination rates, differing greatly from one A-number to the next and from one non-EU location to another.
Over time, more differences in rates arose not just among countries, but also within networks in each country. This made the rate structure and its disparities even more complex, ultimately making calls to the EU from outside the EU much more expensive.
EU Countries Participating in OBR
Since 2015, over 30 European countries have adopted OBR.
This has resulted in 85 service providers implementing OBR across the region.
To illustrate the significant rate disparity and when Caller ID spoofing fraud becomes an issue, consider the following case study:
Case Study: OBR in Portugal
Before OBR, Portugal’s termination rates ranged from €0.0080 to €0.1500, but current rates can reach as high as €0.40868 for mobile traffic via local service providers.
The rate difference between regions is enormous, depending on the A-number country code.
For Example, let's look at the termination rates for mobile traffic in Portugal between different regions under the OBR model with a major local service provider:
| A-number country code | Rate |
| 354 (Iceland) | 0.006 |
| 211 (South Sudan) | 0.08 |
| 244 (Angola) | 0.12 |
| 258 (Mozambique) | 0.28 |
| 245 (Kenya) | 0.41 |
Table showing Portugal's mobile termination rates pre and post-OBR implementation, with substantial differences in charges based on the originating country's A-number code.
You'll notice an almost 70x contrast between the lowest and highest rates by simply changing the A-number. Before OBR, termination rate disparities across most global regions were approximately 20x.
For telcos, this results in an additional 50x fee. In theory, this could have helped local service providers recover losses and increase revenues. Yet, a vital element was overlooked: spoofing fraud. More specifically, a lack of sufficient fraud protection.
Caller ID Spoofing Fraud in the EU Rises: Reasons and Insights
Where there are profits, there is always fraud. Fraudsters quickly realized that the drastic rate differences under the EU’s OBR model provided ideal conditions for Caller ID Spoofing.
Fraudsters didn't need a SIM Box or trunk tampering. They could simply fake numbers, changing non-EU A-number to EU ones, paying local termination rates, and walking away with enormous profits.
So, what could service providers do?
Unfortunately, traditional fraud management systems usually struggle to accurately detect and block call spoofing, creating a challenge for EU service providers. Yet, modern technology offers a solution to halt this issue.
CLI Spoofing and Impersonation Fraud
Impersonation fraud aims to extract sensitive information or money from end-users while causing significant reputational damage to the impersonated brands, making them appear untrustworthy.
How it works: Fraudsters mask the origins of spoofed calls or SMS by using burner phones or software to send texts via emails.
The impact of phone spoofing can be severe. For instance, according to the FTC, Caller ID spoofing fraud caused a total loss of $2.6 billion in 2022, with nearly 200,000 people having already become victims in 2023.
Example #1
In March 2023, a scandal broke out following the Call spoofing scam targeting immigrants in the USA. Fraudsters used fake numbers to impersonate the numbers of Homeland Security Investigations, employing a variety of social engineering techniques, including the threat of deportation, to extract sensitive information and money from victims for malicious purposes.
Example #2
In June 2023, another case emerged where individuals were targeted by an imposter posing as a US Customs and Border Protection Officer. What escalated the seriousness of this CLI spoofing fraud case was that victims discovered the name and Caller ID displayed actually matched that of a genuine officer, intensifying their fear.
Example #3
Today, the FCC warns people to stay vigilant about medical care scam calls. Fraudsters spoof their numbers to appear as trusted health providers. However, the ultimate goal of this Call spoofing scam is to extract personal details like your Medicare card number, Social Security Number, or health insurance ID.
Example #4
In another recent case, CLI spoofing involves student loan scam calls. Fraudsters pose as representatives of a student loan forgiveness program, requesting personal information such as Social Security numbers and bank account information. They might also demand payment over the phone to "process" the loan forgiveness application.
With an understanding of the growing threat of CLI spoofing fraud, let’s see the resulting consequences.
The Impact of CLI Spoofing Fraud
CLI spoofing fraud is a prevalent source of damage to organizations and individuals:
- Destination network operators targeted by CLI spoofing fraud experience revenue loss, inter-operator billing disputes, and eroded customer trust. This weakened trust and potential customer churn negatively affect user lifetime value, forcing end-users to switch to alternative network providers or opt for OTT applications.
- Individual victims of CLI spoofing fraud face the risk of monetary fraud, exposure to unsolicited content exposure, and personal information and identity theft.
So, what solutions can help you overcome these challenges? While various approaches exist, some lack essential requirements for complete protection.
Let’s take a look.
Drawbacks of Conventional Approaches to CLI Spoofing Fraud Prevention
There are three widely used Fraud Management solutions that claim to provide effective protection from Caller ID spoofing, but each has significant limitations.
- Conventional post-factum Call Detail Records (CDR) analysis: falls short in preventing fraudulent calls from connecting.
- Solutions based on databases of unallocated and high-risk numbers: Our recent study showed that these databases offer limited protection, covering 25% of all attacks, while half involve genuine subscribers whose numbers aren't included in any existing database.
- Test Call Generator (TCG): While effective for route assessment, it serves as a complementary spoofing fraud solution rather than a comprehensive CLI spoofing prevention measure. TCG can’t authenticate originating numbers for actual user calls, consequently lacking real-time blocking capabilities.
Overall, none of these solutions can detect and block spoofed calls in real time.
This forces operators to absorb the expenses of spoofing attacks to prevent customer churn. According to the 2021 CFCA Fraud Loss Survey, Caller ID spoofing fraud losses were estimated at around $2.63 billion annually.
The figure not only reflects direct interconnect losses but also considers the broader impact of CLI masking, including indirect losses like customer churn and disagreements over interconnect agreements.
How to Stop Call Spoofing Attacks: The AB Handshake CLI Spoofing Prevention Solution
AB Handshake understands the challenges of addressing CLI spoofing across national and international traffic. Leveraging its expertise, AB Handshake has developed a comprehensive approach to prevent Caller ID spoofing. This multi-layered solution integrates diverse modules, including:
- Real-time bilateral Call Validation
- Advanced AI engine
- Roaming status check
- Cutting-edge next-gen Test Call Generator
Call Validation for CLI Spoofing Protection
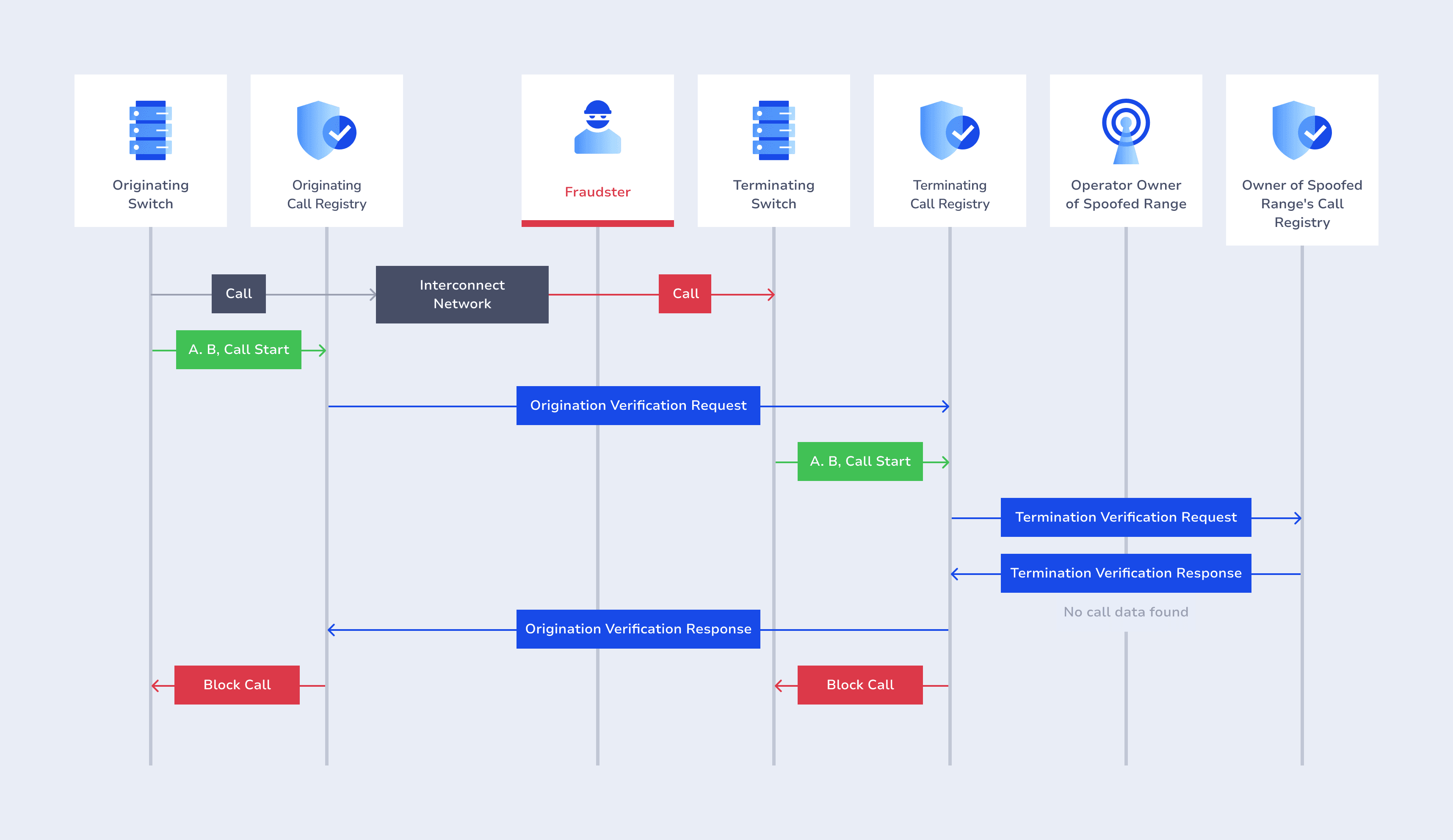
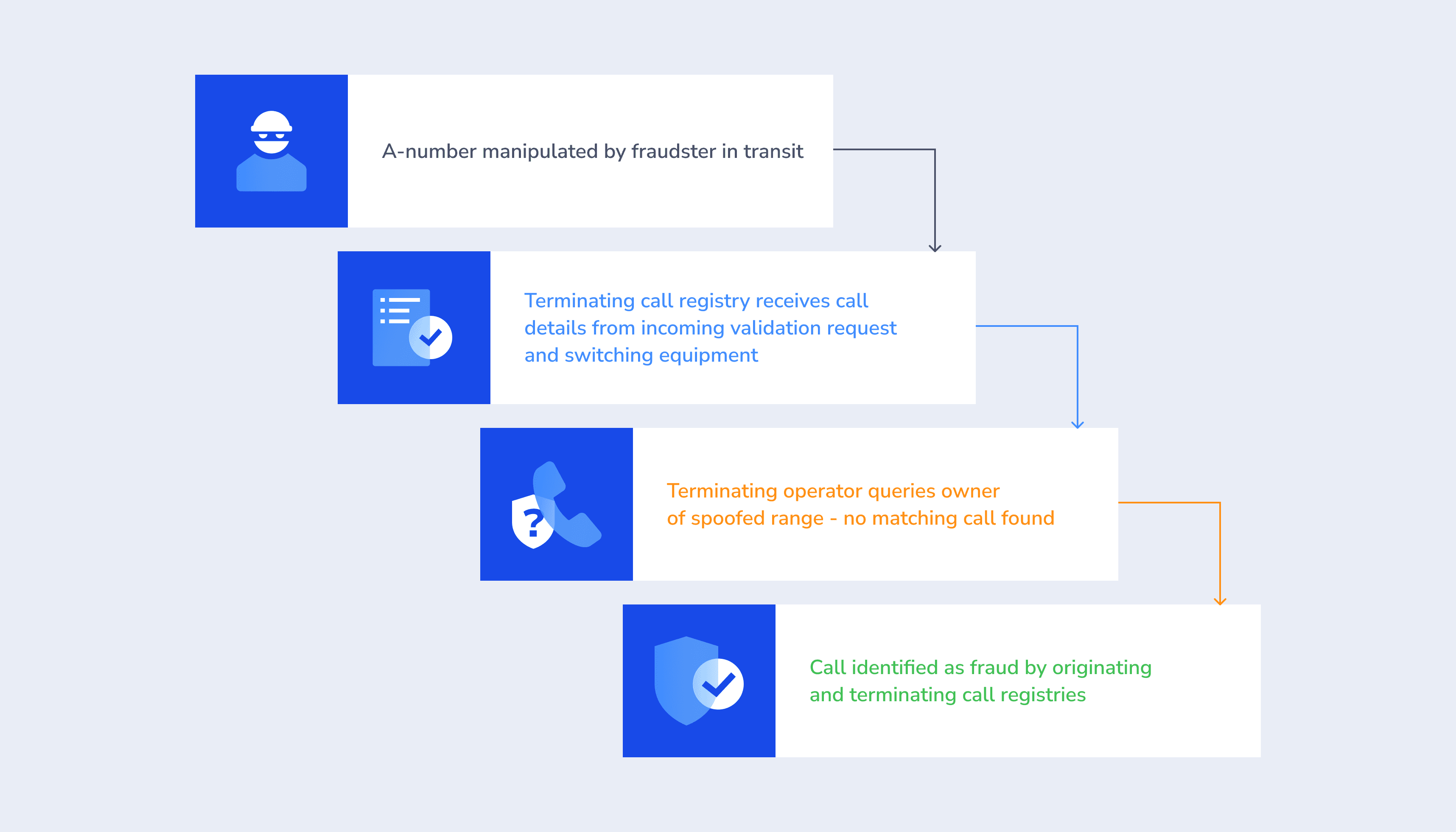
At the core of AB Handshake's innovation is its patented Call Validation technology, which provides real-time, out-of-band, end-to-end call detail validation. This empowers operators to identify the original A number and any manipulation.
We immediately detect and prevent CLI spoofing fraud.
Our Call Validation technology aligns with the latest ITU committee insights, emphasizing the need for a shift from traditional, ineffective threshold-based rules and other isolated solutions to a unified, global real-time validation system. As the ITU urges immediate action towards such innovative solutions, AB Handshake is at the forefront, offering the exact real-time, out-of-band validation required to counteract the sophisticated telecom fraud challenges globally.
Explore the ITU committee's communiqué for an overview of their fraud directives in detail.
The results of our solution are self-evident, considering its widespread utilization by our partners, like Cataleya and more
Communication Shield against Caller ID Spoofing Fraud Enabled by AI
Further strengthening our validation is an advanced AI Shield that excels at identifying even the smallest deviations in call patterns, effectively blocking number spoofing in real time.
This sought-after solution is adopted by operators globally and comes recommended by CEPT as an effective measure for countering CLI Spoofing fraud
Additional CLI Spoofing Protection Methods
For better protection, AB Handshake offers a roaming status check and a next-gen Test Call Generator, providing silent-mode calls from any country prefix to genuine end-users without any disruption.
Looking to protect your traffic from spoofed calls?
Book a meeting with our team, and we’ll answer all of your questions regarding Caller ID spoofing and AB Handshake’s CLI spoofing solutions.